Security
-
5 Things to Look for with Reliable Web Security

Posted on 27 Feb 2022 by Michelle
Security scams and cyber attacks of all kinds are unfortunately inevitable in our web-based world. To make matters worse, scammers are becoming increasingly creative with sneaky cyber threats and attacks. As a result, business owners and in...read more
-
Use https:// when writing a blog post for secure WordPress

Posted on 11 Sep 2013 by Matt Russell
Blogging. A way of expressing your thoughts, ideas, emotions, achievements and so much more online. And WordPress makes building and maintaining your own blog so easy that any other blogging platform is almost a no-brainer. You can be up an...read more
-
What are the security downsides to hosting static third-party content on a subdomain?
Posted on 23 Apr 2012 by Tavis.H
Anytime you host content uploaded by a third party, you run the risk of exposing your server to malicious files or even to hackers who exploit weaknesses in a user’s account. One possible way to avoid this situation is to host the thi...read more
-
PCI DSS and Incident Handling: What is required before, during and after an incident
Posted on 17 Jun 2009 by
Warning: printf(): Too few arguments in /home2/blogwebhostingbu/public_html/wp-content/themes/webhostingbuzz-blog/tag.php on line 22
I found this great article today in the SANS Internet Storm Center Reading Room and thought I would post a link to share with our readers. PCI DSS and Incident Handling: What is required before, during and after an incident. It can not be s...read more
-
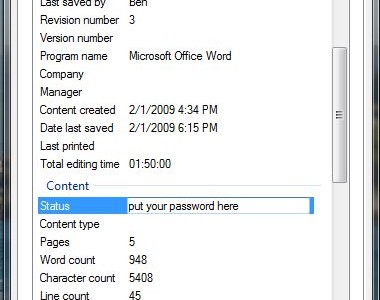
Managing Too Many Passwords
Posted on 29 May 2009 by
Warning: printf(): Too few arguments in /home2/blogwebhostingbu/public_html/wp-content/themes/webhostingbuzz-blog/tag.php on line 22
In my previous post (Complex Passwords for Complex Security) I detailed the importance of complex passwords. After posting, I thought of all the passwords we have to remember, and felt like I should post an addition to it. By no...read more
-
Proper Ways to Destroy Private Data and Sanitize Hard Drives
Posted on 28 May 2009 by
Warning: printf(): Too few arguments in /home2/blogwebhostingbu/public_html/wp-content/themes/webhostingbuzz-blog/tag.php on line 22
To continue this week’s security focus, today we’re going to talk about how to securely delete sensitive data off of old hard drives. All businesses must make it a top priority to protect their customer’s private informati...read more
-
Complex Passwords for Complex Security
Posted on 27 May 2009 by
Warning: printf(): Too few arguments in /home2/blogwebhostingbu/public_html/wp-content/themes/webhostingbuzz-blog/tag.php on line 22
There are hundreds of ways to make your site or network more secure. These can involve expensive hardware, complicated software, and a LOT of research and time to develop and implement. What’s a low-cost way to beef up your security? ...read more
-
A Security Mindset
Posted on 22 May 2009 by
Warning: printf(): Too few arguments in /home2/blogwebhostingbu/public_html/wp-content/themes/webhostingbuzz-blog/tag.php on line 22
I was at a brand new Taco Bell this afternoon with my girlfriend when I noticed an interesting problem: the new drink dispenser had four drinks per spout, with a button that selected the drink you wanted dispensed. I’ve obviously been...read more
Notice: Undefined variable: loop in /home2/blogwebhostingbu/public_html/wp-content/themes/webhostingbuzz-blog/tag.php on line 29
Notice: Trying to get property 'max_num_pages' of non-object in /home2/blogwebhostingbu/public_html/wp-content/themes/webhostingbuzz-blog/tag.php on line 29




